About eScan
MicroWorld develops Information Security solutions that provide protection against current and evolving cyber threats. Our product portfolio includes eScan and MailScan that encompass Anti-Virus, Anti-Spyware, Content Security, Anti-Spam and Network Intrusion Prevention solutions. Incorporated in the USA with offices worldwide, we are represented by our partners across the globe.
Headed by the dynamic entrepreneur and technocrat, Mr. Govind Rammurthy, MicroWorld began operations in the year 1993. Since then, we have been pioneers in the development of Information Security solutions and been an active contributor to the industry in combating complex and evolving IT threats.
MicroWorld’s products cover the entire security spectrum, making it a one-stop solution for protecting all your information security assets. Over the years, MicroWorld has been redefining the Information Security landscape by developing innovative technologies and solutions. Our continued endeavor is to provide Futuristic Security Intelligence to computers; be it in an Enterprise, SMB, or even Home solutions.
eScan has been rewarded under the standards of ISO 9001, ISO 14001 and ISO 27001 by Euro Veritas Certification, a global certification leader. This certification is a significant milestone in eScan’s commitment towards providing the highest quality of products and services and continuous efforts to improve the technological advancements and product development.
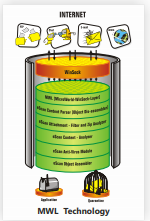
MicroWorld Winsock Layer (MWL) Technology
MicroWorld-WinSock Layer (MWL) is a revolutionary concept scanning Internet traffic on a real-time basis. It resides on the Winsock Layer of the Operating System and scans all the incoming and outgoing traffic from and to the Internet. It
checks content for security violations and passes all the clean data packets to the application layer, whereas
blocks the rest.
MWL that is placed above the WinSock layer, in other words, acts as a ‘ Transparent Gatekeeper’. All the data packets coming on relevant TCP / IP ports are assembled and decoded, be it e-mail, web, FTP or ICQ traffic. The decoding
logic divides the data into body & attachments and passes the same through numerous filters such as Virus Filters, Content Filters, Attachment Filters, etc. These filters check validity of the content and, depending on the results of the validation, the packets are either accepted or discarded. The User is also notified of any packet drops, using dynamic notifications.
Proactive Behavioral Analysis Engine
Proactive Behavioral Analysis Engine monitors the activity of all processes on Local Machine and when it encounters any activity or behavior that matches to a ransomware, a red flag is raised and the process is blocked. In case if an infected system tries to access network share of a protected system and encrypt/ modify files residing on that system, PBAE will immediately invalidate the network session, PBAE is successfully blocking ransomware attacks such as Locky, Zepto, Crysis and many more. Additionally, by analyzing the data collected through our Cloud (ESN) we are able to successfully detect and mitigate thousands of ransomware attacks on every system that is protected with eScan.
Host Intrusion Prevention System (HIPS)
The system monitors all network activities and not only warns about any intrusion, but also blocks it. It uses both, signature based detection as well as advanced heuristics Anti-Virus algorithm, and allows you to set policies specifying the behavior of OS or applications. The system protects against viruses, spam, Spyware, worms, Trojans, Keyloggers, Bots, Rootkits, Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks.
Domain & IP Reputation Check
This check verifies the credibility of Web domains by tracking any indication of suspicious activities on the web page. It also verifies the integrity of the IP address by comparing it with a list of known email senders using a service that assesses the senders reputation in real-time. Emails received from domains with malicious activities are not accepted.
Non-Intrusive Learning Pattern (NILP) Technology
NILP works on the basis of Artificial Intelligence where it learns the user’s behavior and takes an informed decision. It helps identify and classify mails on behalf of the users, whether the mails are spam or ham.
eScan Security Network – Cloud Based Technology (ESN)
eScan Security Network is a state-of-the-art technology implemented in the latest versions of eScan range of Security
Solutions. eScan’s cloud-based Security Network collects information from millions of eScan participants from around
the world when they are online, to safeguard your digital world from the latest threats. When it comes to new malware, it ensures a prompt response and an advanced level of detection that provides superior protection. eScan Security Network not only allows previously unknown threats to be detected and blocked but can also locate and prevent zero-day threats and phishing attempts.
Advanced Virus Control (Smart Proactive Protection)
With its new Advance Virus Control technology and highly sophisticated Heuristics Algorithms, eScan effectively scans
and detects unknown malware that are continuously released by malware writers. It not only detects, but also warns users about applications that behave in a suspicious manner, thus providing protection from Zero-Day threats. eScan even allows blocking of files from being accessed, either locally or via the network, thus further preventing network-based viruses from infecting all the connected computers.